Web Security Projects
Description
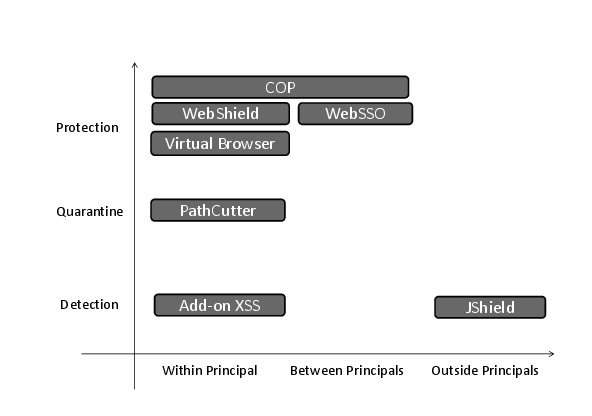
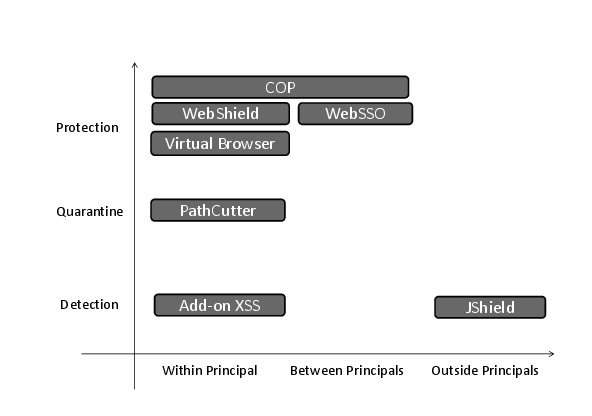
We have built a principal-based browser architecture to detect, quarantine, and
prevent various web-borne security threats, which happen within, across, and
outside web principals. We define a web principal, as borrowed from operating
systems, an isolated security container of resources inside the client browser.
To understand the aforementioned web-borne security threats, we have proposed
using crowdsourcing techniques to detect patterns of intra-principal
threats, i.e., add-on cross-site scripting (XSS), as well as vulnerability signatures to
detect patterns of an
outside-principal threat, i.e., drive-by download attacks.
We propose a
two-step prevention mechanism, which first proactively quarantines those
threats, and then, reactively modifies and protects existing infrastructures
from those threats. My proactive approach quarantines XSS attacks inside iframes
to cut off their further propagation path; my reactive
approaches first redefines web browser principal boundaries by a new client-side access
control policy, then make those client-side principals stronger by either
virtualization or proxy, and at last connect those
principals by a secure channel. The classification of the Web security is shown in
the figure.
People
Collaborators
Publication
-
Xiang Pan, Yinzhi Cao, and Yan Chen, I Do Not Know What You
Visited Last
Summer - Protecting users from third-party web tracking with
TrackingFree
browser,
in the Proc. of Internet Society NDSS Symposium, 2015 (50/313 = 15.9%).
-
-
Yinzhi Cao, Xiang Pan, Yan Chen and Jianwei Zhuge, JShield: Towards Real-time and Vulnerability-based Detection of Polluted Drive-by Download Attacks, in the Proc. of Annual Computer Security Applications Conference (ACSAC), 2014 (19.9%).
-
Presentation PowerPoint
- Adopted by Huawei, the world's largest telecommunication equipment maker, in their high-end Web Firewall products.
- Yinzhi Cao, Vaibhav Rastogi, Zhichun Li, Yan Chen, and Alex Moshchuk,
Redefining Web Browser Principals with a Configurable Origin Policy, to appear in the Proc. of The Annual IEEE/IFIP International Conference on Dependable Systems and Network - Dependable Computing and Communications Symposium (DSN - DCCS), 2013 (21/107=19.6%).
-
Xun Lu, Jianwei Zhuge , Ruoyu Wang, Yinzhi Cao, and Yan Chen,
De-obfuscation and Detection of Malicious PDF Files with High Accuracy, in the Proc. of Hawaii International Conference on System Sciences (HICSS), 2013.
-
Yinzhi Cao, Zhichun Li, Vaibhav Rastogi, Yan Chen, Xitao Wen, Virtual Browser: a Virtualized Browser to Sandbox Third-party JavaScripts
with Enhanced Security , in the Proc. of ACM Symposium on
Information, Computer and Communications Security (ASIACCS), 2012 (35/159=22%, full
paper).
-
Presentation PowerPoint
-
Yinzhi Cao, Vinod Yegneswaran, Phil Porras, Yan Chen,
PathCutter: Severing the Self-Propagation Path of XSS JavaScript Worms in Social Web Networks, in
the Proc. of 19th Network & Distributed System Security Symposium (NDSS),
2012 (46/258=17.8%).
-
Presentation PowerPoint
-
Zhichun Li, Yi Tang, Yinzhi Cao, Vaibhav Rastogi, Yan Chen, Bin Liu, Clint Sbisa,
WebShield: Enabling Various Web Defense Techniques
without Client Side Modifications, in
the Proc. of 18th Network & Distributed System Security Symposium (NDSS),
2011 (28/139=20%).
-
Presentation PowerPoint